|
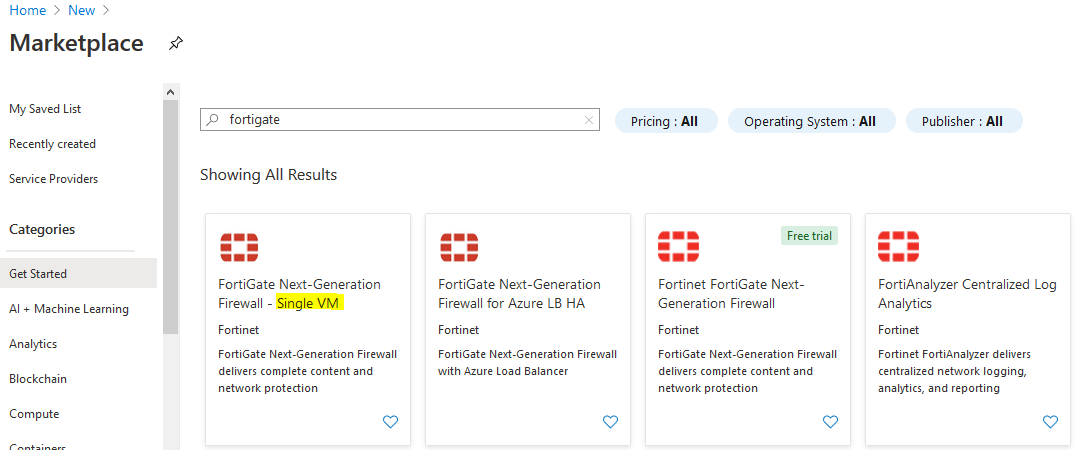
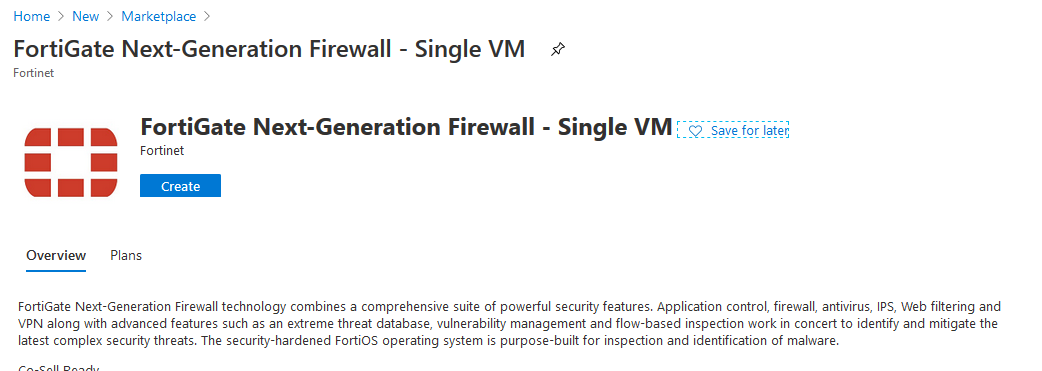
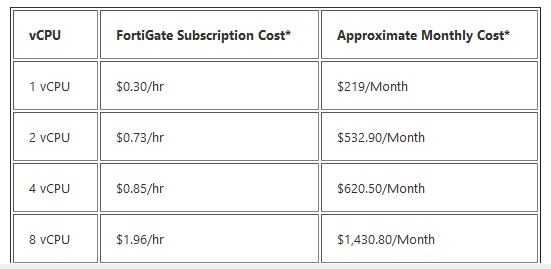
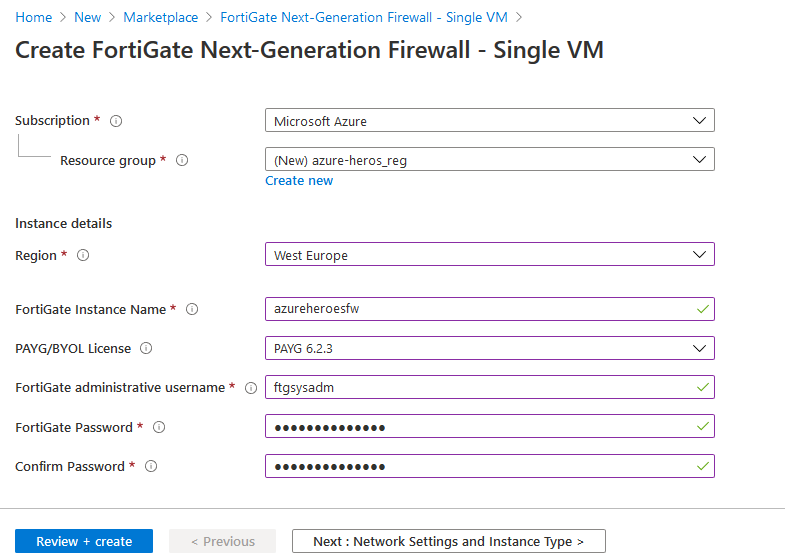
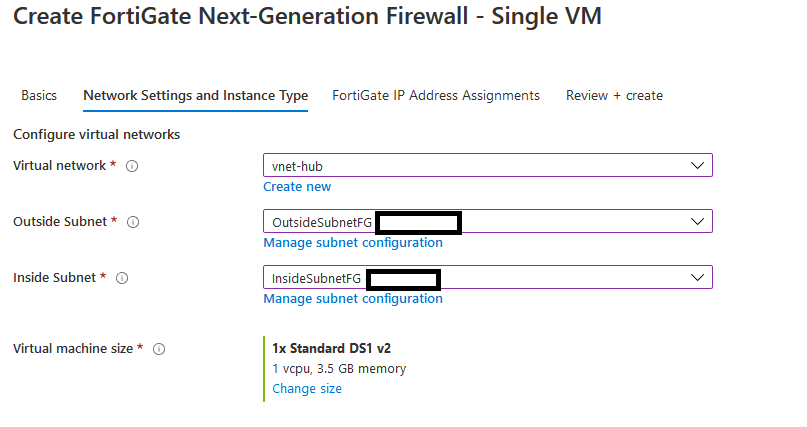
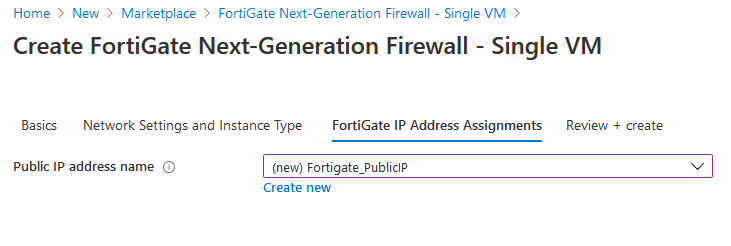
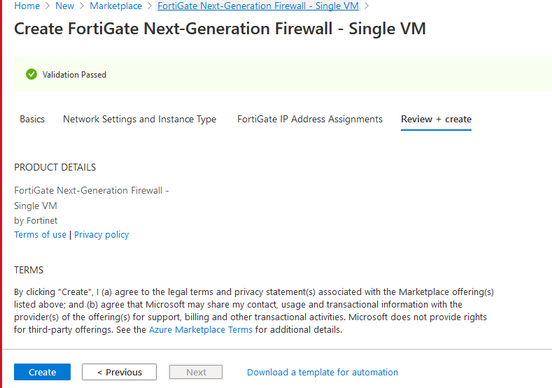
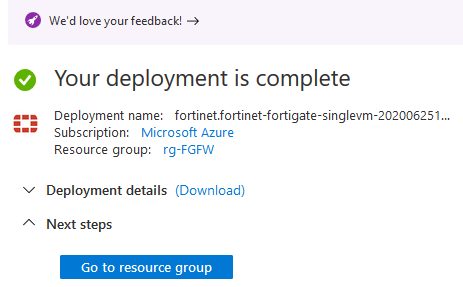
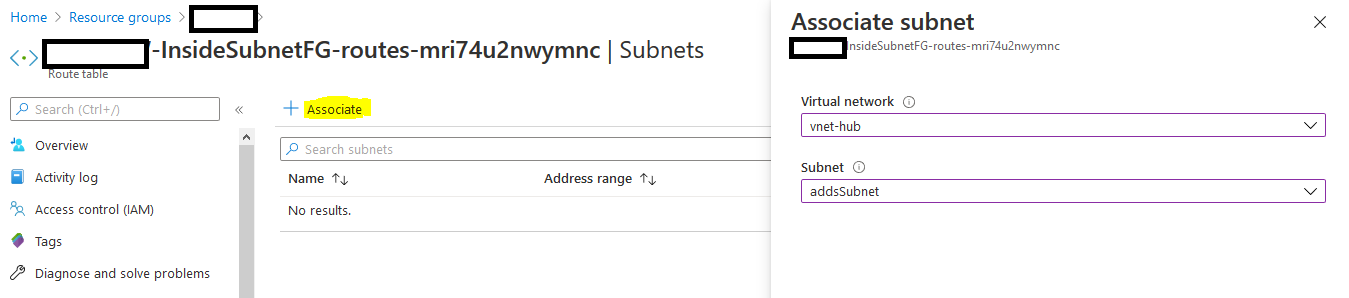
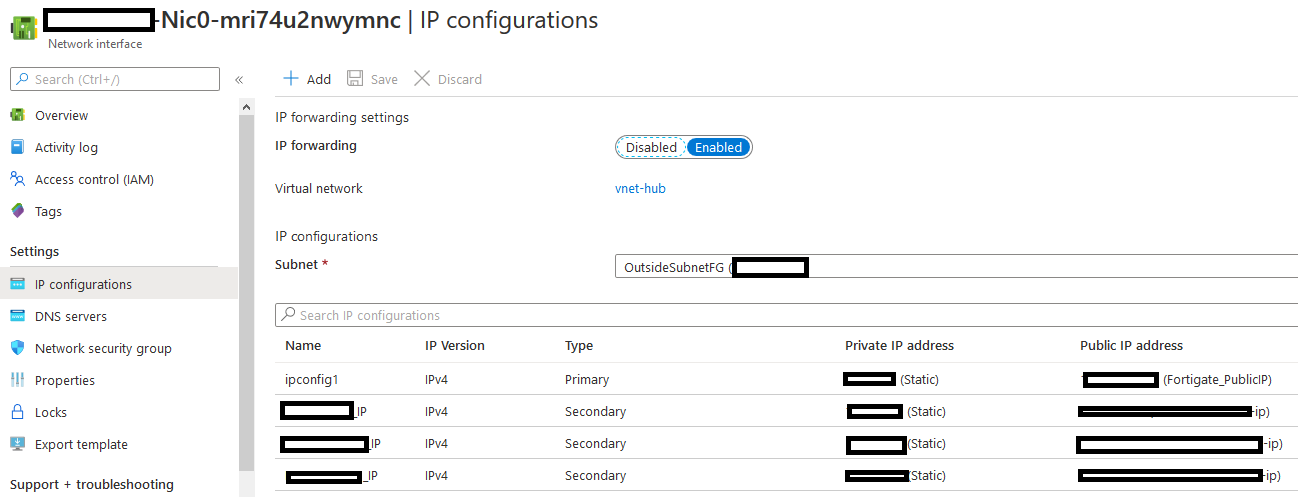
Azure Firewall is a managed, cloud-based network security service that protects your Azure Virtual Network resources. It's a fully stateful firewall as a service with built-in high availability and unrestricted cloud scalability. As I haired from a few customers that Azure firewall is a little bit expensive! and some of them they don't have a budget for test/dev environment,as it cost (approximately $100 monthly, per appliance). This price gets compounded if you need to deploy multiple Azure Firewall appliances per regional VNet In this post we will explain how to deploy FortiGate NGFW for Azure, you can deploy the FortiGate for Azure as a virtual appliance in Azure cloud (infrastructure as a service) This section shows you how to install and configure a single instance FortiGate-VM in Azure to provide a full NGFW/unified threat management (UTM) security solution in front of Azure IaaS resources Deployment Current Environment: I have around 15 VMs, connected to the same VNet which it has around 12 Subnets I created another two subsets for FortiGate VM as i will explain later
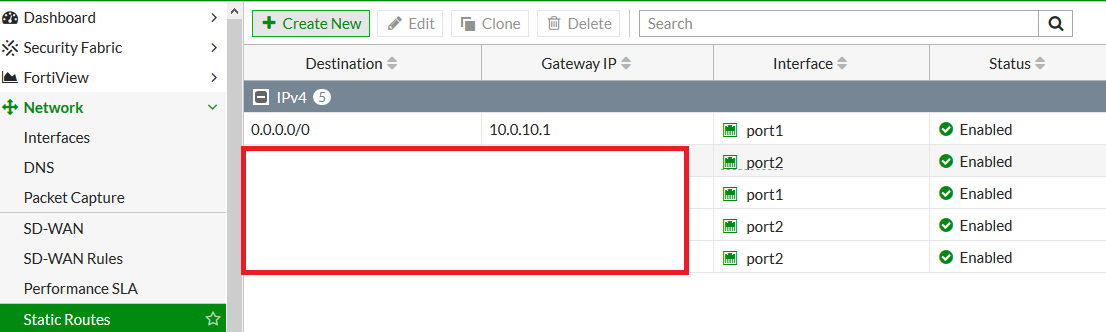
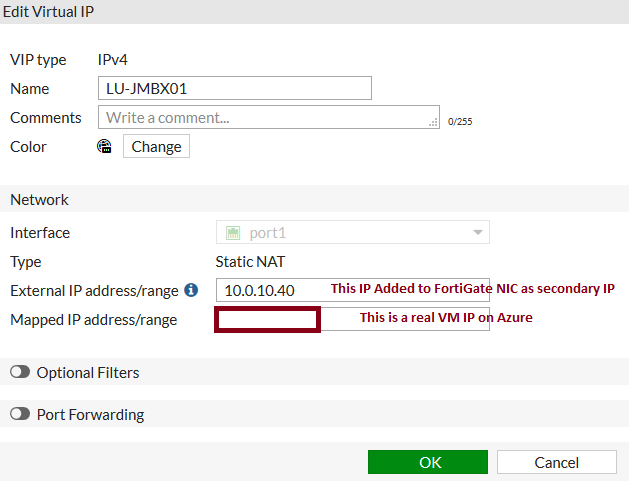
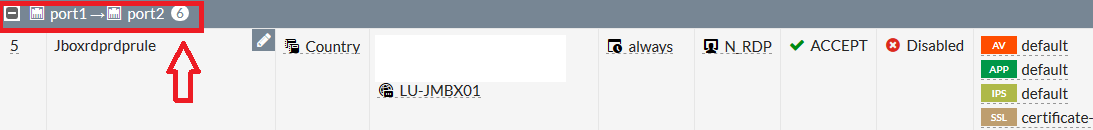
Allow Inbound Traffic: Let's consider I have an jump server and I need to allow outbound port# 3389, this first thing I will do is
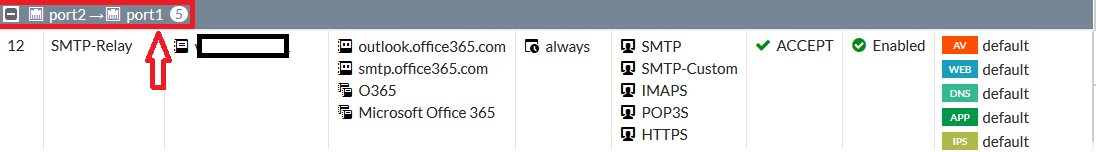
And in case you want to allow outbound traffic do the same but, from port2 to port 1 as per the below screenshot
10 Comments
Mostafa agha
6/25/2020 11:17:50 pm
Keep good posts
Reply
Rousan
6/28/2020 11:20:18 pm
I will, Thank you :)
Reply
Mostafa Elshahat
6/28/2020 11:12:07 pm
good job , very clear
Reply
Rousan
6/28/2020 11:20:46 pm
Thank you my dear :)
Reply
Saravanan
7/18/2020 01:40:09 am
Good job , thanks for sharing
Reply
Babajide
10/15/2020 03:19:18 pm
Thanks for the post. i need clarification the last part how do i protect the VM in azure using the fortigate, how tdo i route traffic through fotigate before getting to the Azure VM
Reply
Mohammad Al Rousan
10/16/2020 02:43:28 pm
Reply
Babajide
10/16/2020 02:08:37 pm
Can you please show me how you created the static route in fortigate and how you were to RDP into the 3 VMs using the IP attached to fortigate NIC since they are not attached to the VM itself
Reply
Mohammad Al Rousan
10/16/2020 02:46:13 pm
If you want to Map one public IP to the 3 VMs then you have to use Azure Load balancer (NLB) as there is a limitation on Azure to map one public IP to multiple VMs
Reply
Kong Tuck Chee
11/9/2021 01:12:14 pm
Isn't this more costly than Azure VPN Gateway ? Azure VPNGW1 plan is only USD136.80 per month while Fortgate FW cheapest plan is USD $219/month. Correct me if i am wrong. I never deploy Fortigate in Azure before.
Reply
Leave a Reply. |
Author
Mohammad Al Rousan is a Microsoft MVP (Azure), Microsoft Certified Solution Expert (MCSE) in Cloud Platform & Azure DevOps & Infrastructure, An active community blogger and speaker.
Al Rousan has over 8 years of professional experience in IT Infrastructure and very passionate about Microsoft technologies and products. Top 10 Microsoft Azure Blogs
Archives
September 2023
Categories
All
|



 RSS Feed
RSS Feed
